When you’re looking at the most important things to consider when running a site, security is right up there at the top of the list. If you can’t guarantee the safety of your data and data of your users, you probably won’t get far. Putting up a site, blog or webshop doesn’t automatically mean that the person or company doing it has the technical knowledge to handle security matters themselves.
Because of this, the best solution would be to delegate this task to somebody who has the knowledge and experience to do everything that needs to be done without involving you in the process anymore that is absolutely necessary. Most of the time these are specialized internet security services, but what about combining your hosting and security services into one.
We’ll go over some standard (and less standard) security features that any commercial site should have and compare it to the security features provided by Kinsta.
[bctt tweet=”#Kinsta is a #hosting service that takes all the worries out of your hands and takes care of everything for you. @kinsta”]
In doing so, you can focus solely on the content you wish to promote and let someone else worry about everything else.
Table of Contents
Two-factor authentication
Looking at it from the user standpoint, the login is, at the same time, the first place a security breach could happen and possibly the one most at risk (both for them and for you). This is where two-factor authentication can help you. This is a security method that confirms the user’s identity by using, as the name suggests, two different variables.
The first one is always the same – you have to enter your password. The second one can vary and can be, somewhat crudely, divided into:
- Physical authentication – the earliest form of a second-factor authentication, tokens were handed out by banks so you could manage your money, cards, and accounts away from their subsidiaries. For those of you who have never come in contact with them, they’re like tiny calculators that provide you with a six-digit code that changes every 30 seconds. The main reason they aren’t used as widely as before is the manufacturing cost – they’re physical, and practicality (or lack thereof) of use. With technological advancements, we get to the following options…
- Phone authentication – most commonly an SMS is used for authentication, but they can also (very rarely) be voice-based. Concentrating on the SMS, it works similarly to the token. You’ll get a code in a text, that you’ll then input and be granted access. Currently, this type of authentications is being phased out since it was found to be the least reliable way for both users and providers.
- Software authentication – nowadays this is the widest spread form of authentication. You’ll have to download the app and through it get one-time passwords that you’ll use with your login name and password. Right now it’s the safest and most practical form of authentication out there, and since basically everybody uses smartphones, you’ll be able to use it anytime and anywhere.
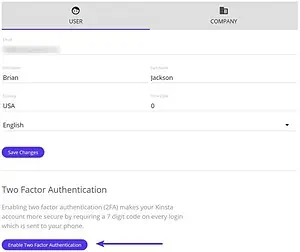
With Kinsta you’ll have the option of an SMS authentication which is sent directly from the MyKinsta dashboard and a software authentications using an app from Authy – their longtime collaborators in these matters.

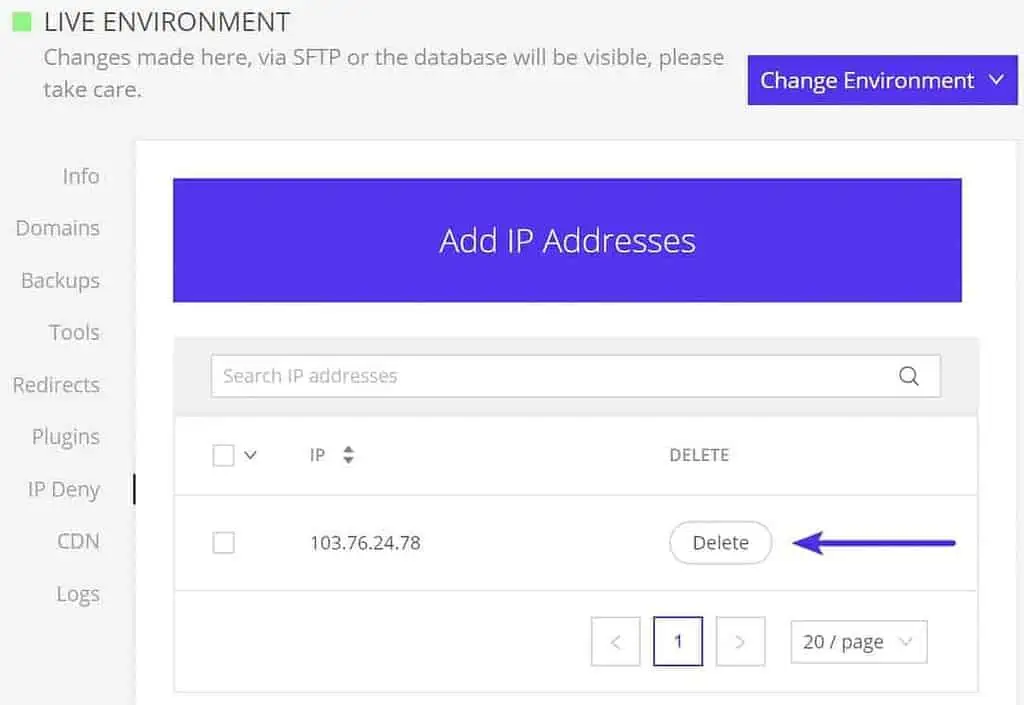
IP blocking
When running a commercial site, you’ll probably be a target for various bots, spammers and hackers. The more exposed and successful you become, the bigger target you make. Even if they don’t break through and don’t compromise your information, the sheer number of requests can seriously impact your operating capacity discouraging the regular user from visiting your site. This is why IP blocking is very important as security measures go. Blocking an IP address(es) prevents it from even sending any requests leaving your information safe and your bandwidth intact.
With Kinsta you’ll be able to access a detailed IP analysis that will help you pinpoint potential spammers and/or bots. You’ll see the analysis both by IP geolocation and individual requests made.
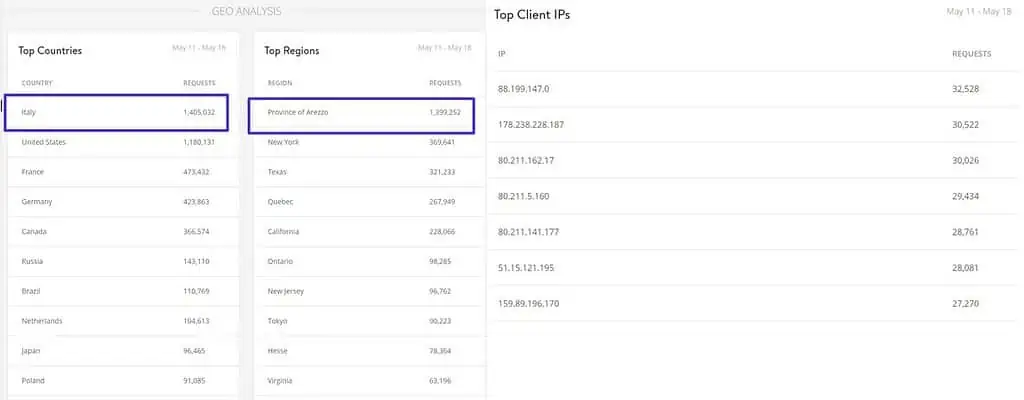
If anything seems suspicious you’ll be able to deny a certain IP address and then just monitor traffic for the next couple of days to see if the problem is resolved.
Working with the Kinsta support team, you’ll also be able to enforce GeoIP blocking and thus deny all request originating from certain countries. This is done if your content conflicts with the country’s regulations or if a vast number of IPs from a certain country proves to be fraudulent.
Encryption and certificates
Without going into too much detail, encryption is used to make your data transfers secure. There are many different protocols that can be used and that have been proven to be successful. Kinsta offers an SFTP and SSH encryption that has proven to be more than adequate, especially when the underlying security infrastructure is sound.
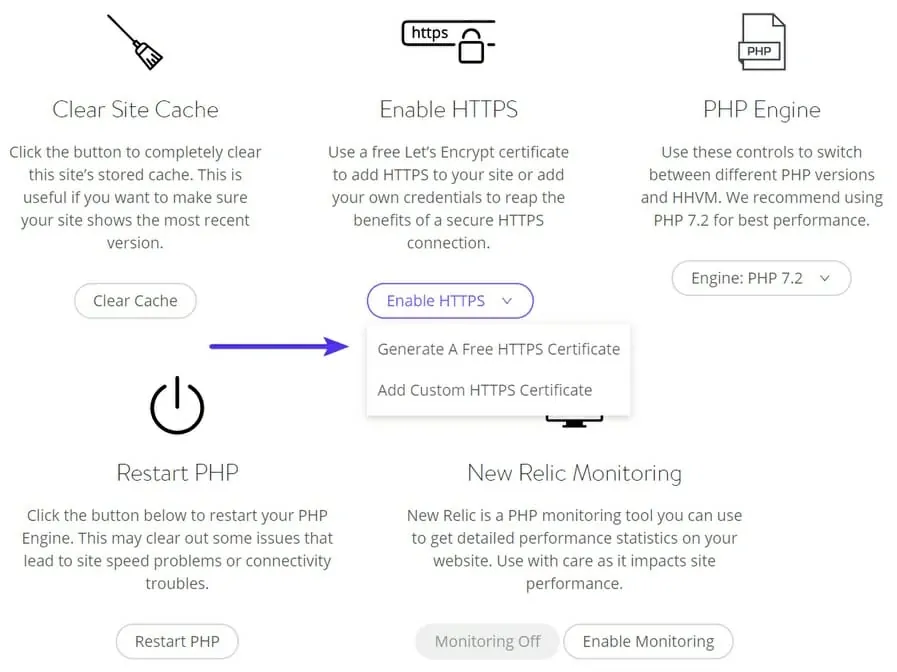
Furthermore, you’ll get free Let’s Encrypt integration allowing you to issue SSL certificates to enable HTTPS. These are important so your site won’t conflict with the security settings of your user’s browser.
Additional Kinsta security features
Moving on from the core security features that essential any and every service out there it’s time to focus on some more specific to our test service.
Probably the perfect example of the level of service that you’ll get is the fact that your site’s uptime is checked every two minutes. That relates to 720 daily checks. Combine it with a 24/7 support service and most of the time any problem that arises will already be in a solving process by the time you even report it which is definitely saying something.
Now it’s fair to say that problems will occur, that’s simply a fact that can’t be avoided. What can be avoided is additional costs, downtime, and data loss. Even here Kinsta has you covered.
If your site is compromised in any way solving the problem becomes a top priority, and the whole process is absolutely free. Downtime in these situations is a non-issue because your site is backed up daily (and for additional fees can be bumped up to an hourly basis). These backups are stored in two-week intervals, so rolling back a compromised site can be done instantly, even while the problems are being sorted out.
Summary
All of us are looking for ways to ease our business as much as we can. This means using services that, after they’re bought and paid for, we don’t even want to hear about. Kinsta is one of those services. They provide hosting to your site(s) with a security and support background that need minimal input from you, making it so you can focus on other things.
With core security methods all in place, all aspects of the service constantly updated and 24/7 support if you do have worries it won’t be about security, so be sure to check them out.