Updated on
Different industries, different hosting providers, different budgets – yet the root causes repeat in surprisingly familiar ways. Updates quietly drift behind, access accumulates over time, bots generate noise nobody looks at closely, and backups exist in theory but haven’t been restored in years.
This week’s roundup isn’t about dramatic attacks or clever exploits. It’s about the quieter patterns that cause most real-world problems. If you recognize a few of them on your own site, that’s normal. The goal isn’t perfection – it’s building a baseline that prevents the most common issues before they turn into incidents.
When people imagine WordPress security problems, they often picture a single dramatic failure – a clever attacker exploiting some obscure vulnerability.
In practice, that almost never matches what we see.
Most incidents develop slowly. Small gaps appear, nothing breaks immediately, and over time those gaps begin to overlap in ways nobody planned. By the time someone notices something unusual, the problem has usually been building quietly for weeks or months.
That’s why recognizing the patterns early is more useful than memorizing long checklists.
Here are some of the ones that show up again and again.
Pattern 1: The update that kept getting postponed
Outdated plugins and themes remain one of the most common entry points for compromises, but it rarely happens because someone consciously decided to ignore updates.
More often the story looks like this: an update appears on Monday, you plan to install it later, something else becomes urgent, and by the time you remember again there are five updates waiting instead of one.
The longer updates drift behind, the more likely it becomes that one of those releases quietly included a security fix. From the outside it looks like a vulnerability was exploited. From the inside it usually looks like a normal week that simply got busy.
The practical approach here isn’t complicated: keep WordPress core, plugins, and themes on a consistent update rhythm, remove anything you’re not actively using, and pay attention to plugins that haven’t been maintained for a long time.
Security problems rarely begin with a dramatic mistake. They usually begin with something small that stayed unresolved just a little too long.
Pattern 2: Access slowly becomes messy
Another pattern appears when access control evolves over time without anyone really reviewing it.
An agency account from a previous redesign.
A contractor login that was never removed.
A shared administrator account used by several people.
An admin account without two-factor authentication because “it was just temporary.”
None of these decisions look dangerous in isolation. Each one makes sense at the time.
But after a year or two the site might have far more administrative access than anyone realizes, and at that point the problem isn’t a clever attack – it’s simply that too many doors exist.
Keeping admin accounts limited to the people who genuinely need them, using strong unique passwords, and enabling 2FA for administrative users eliminates a surprising number of potential issues before they even begin.
Pattern 3: No visibility when something changes
One of the most frustrating situations during an investigation is discovering that nobody can answer basic questions about what happened.
Who logged in?
What changed first?
When did the suspicious behavior begin?
Without logs or monitoring, those questions turn into guesswork. People start reconstructing events from memory or trying to interpret small clues scattered across the site.
That uncertainty is often what turns a small problem into a long investigation.
Adding visibility – through logging, monitoring, or security scanning – doesn’t prevent every issue, but it dramatically reduces the time needed to understand what’s actually happening when something feels off.
Pattern 4: Security becomes something you “installed once”
Another pattern shows up in how people think about security itself.
A plugin gets installed, a few settings are configured, and the task feels finished. Security becomes something that was “taken care of” at some point in the past.
In reality, security behaves less like a one-time project and more like a quiet maintenance loop: establish a baseline, fix the obvious issues, monitor changes, and revisit the setup occasionally.
That loop doesn’t need to be complex. Even a short weekly or biweekly review is enough for many sites. The important part is treating security as something that evolves alongside the site itself.
Pattern 5: Bots that slowly become an operational problem
Many site owners assume that if bots aren’t breaking into the site, they aren’t really causing harm.
But bot traffic often creates a different kind of problem: operational noise.
Repeated login attempts, automated requests to random URLs, and endless probing for vulnerable plugins can quietly increase server load and cause intermittent slowdowns. Over time this kind of traffic can make a site feel unreliable even though nothing has technically been “hacked.”
Reducing abusive patterns early – through firewall rules, rate limiting, or blocking repeated offenders – helps keep the site responsive for real visitors.
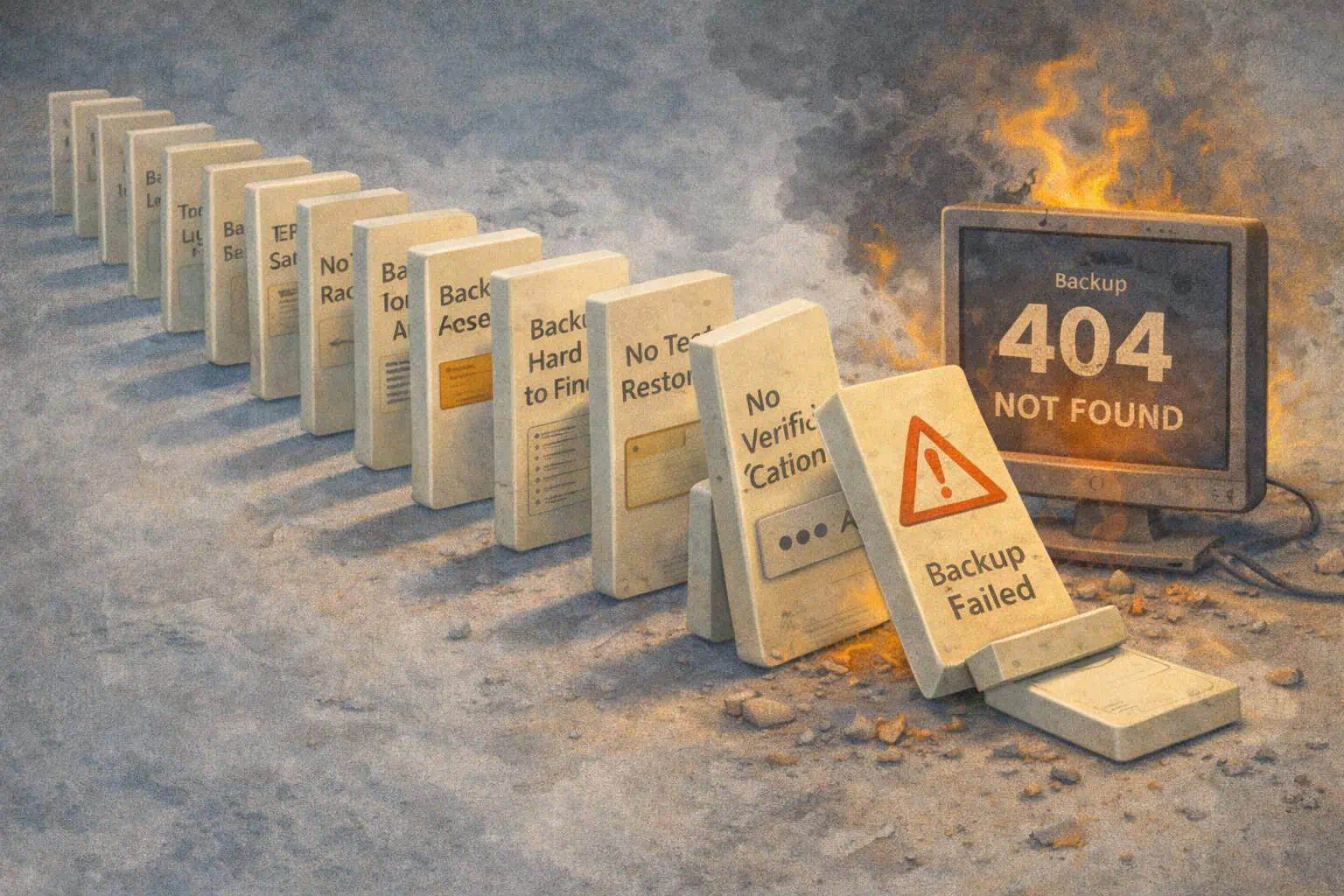
Pattern 6: Backups that exist only in theory
Backups are one of those things everyone agrees are important, which is exactly why they often go untested.
The moment when backups matter most is usually the first time anyone tries to restore one. That’s when people sometimes discover that the backups are incomplete, outdated, difficult to access, or stored somewhere nobody can quickly retrieve them.
A healthier baseline is simply verifying once in a while that restoring a backup actually works. Knowing where backups are stored and how they can be restored removes a huge amount of uncertainty when something unexpected happens.
Pattern 7: Fixing security only when something goes wrong
Security work tends to receive attention after an incident, because that’s when the risks suddenly feel real.
But the easiest time to make improvements is when nothing is on fire. Small adjustments made during quiet periods – updating software, tightening access control, enabling logging – prevent many of the situations that later become urgent.
Starting with the most likely issues first keeps the process manageable and prevents security from becoming overwhelming.
Pattern 8: Trying to solve everything at once
One of the biggest traps for beginners is the belief that security requires solving every possible problem immediately.
Long checklists and conflicting advice can easily create the feeling that everything is urgent, which often leads to the opposite outcome: nothing gets done because the task feels too large.
A better approach is a repeatable baseline. For most WordPress sites that baseline is surprisingly simple: keep software updated, limit administrative access and enable 2FA, run security checks periodically, maintain visibility into what changes on the site, and ensure backups can actually be restored.
None of these steps are dramatic on their own.
But together they quietly prevent most of the problems we see in practice.
Get AI-Powered Security Summary
Let AI analyze this WordPress security article and provide actionable insights from WP Security Ninja experts.